How to develop an enterprise cloud strategy

The Committee of Sponsoring Organisations of the Treadway Commission (COSO) has released its Enterprise Risk Management for Cloud Computing report.
The report is authored by Mike Grob and Victoria Cheng from consultancy Crowe and aims to help companies in the early stages of developing a cloud strategy. “Bolstering cloud governance will reduce the organisation’s risk and allow for more efficient and effective use of cloud computing and monitoring in a multi-cloud environment,” they say.
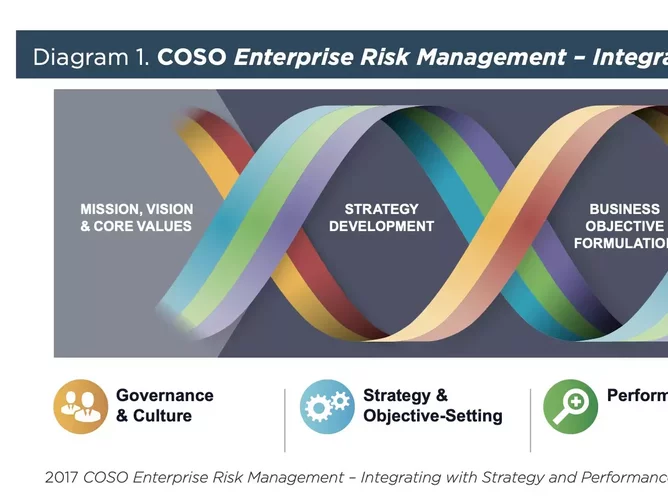
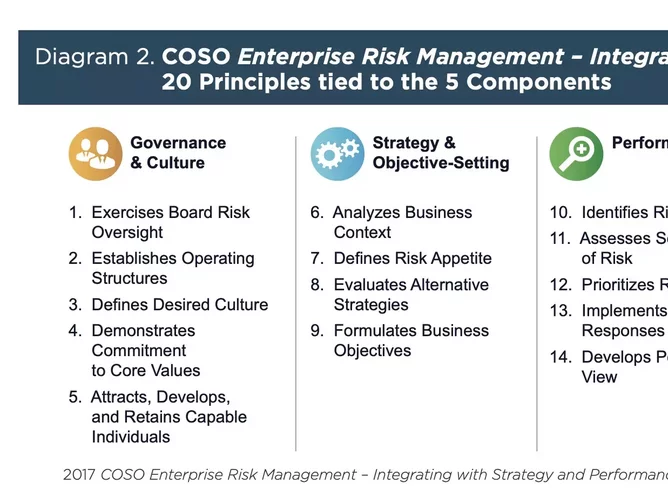
COSO breaks down cloud strategy into five core areas: governance and culture, strategy and objective setting, performance, review and revision, and information, communication and reporting.
The report concludes: “Cloud computing is one of many technology options available for organisations to utilize. A structured adoption of cloud computing, including a holistic cloud computing governance program that addresses the associated risks and is incorporated into the ERM program, will enable an organisation to derive the most value and enable the organisation to achieve its strategic objectives.
“For an organisation to maintain a competitive edge, it will need to use its IT strategy to empower the business. Integrating cloud computing into the IT strategy and turning the IT organisation into a strategic partner can provide many of the tools and framework needed for the organisation to succeed.
“Cloud computing risks must be identified and managed in the context of the organisation’s broader ERM program. While tasks, processes, and maintenance can be outsourced, accountability for risks cannot. The ownership of the risks will remain with the organisation who will need to monitor the internal controls within the organisation and of its CSPs.
In order to use cloud securely, organisations should invest and implement a variety of security tools. The organisation will need to leverage available technology to continue to monitor, report, and update assessments of the cloud computing technology, vendors, and ERM program. Senior management and the governing body should also ensure that the internal audit activity has included cloud-based services in its risk-based planning process, to provide independent assurance and advice.
Cloud governance
“Organisations that have already embarked on the path to cloud computing without an ERM framework can and should still add cloud governance to their processes. Since the cloud governance process should be incorporated into the ongoing activities related to business strategy, IT strategy, and cloud computing, the cloud governance should be continually updated and revised based on new information. If an organisation has not created a cloud governance program, it can do so at any time and continue to refresh as changes occur. By incorporating cloud governance into the organisation’s cloud computing processes, the organisation is better positioned to manage risks that threaten the strategy and objectives of the organisation.
“The use of the COSO Enterprise Risk Management – Integrating with Strategy and Performance framework enables cloud computing to be integrated with the organisation’s ERM function. The cloud computing governance approach provides a holistic view of cloud computing throughout the organisation. Governance and communication and reporting dovetails with the cloud strategy, performance, and monitoring and revision. This is undertaken with a view that the implementation of cloud computing will coalesce the CSP’s cloud computing governance processes with those of the organisation.”






