SAP innovating to secure the world’s largest private cloud
The use of the cloud has truly taken off in recent years, but as cloud computing increases, so too do security threats. For companies such as SAP, which operates a private cloud, protecting the data of their customers is absolutely critical.
Roland Costea, the Global Chief Security Officer for SAP’s Enterprise Cloud Services, is responsible for running the Global Cybersecurity Program and Strategy for SAP’s Private Cloud.
“SAP is the coolest software company that your friends have never heard of,” he explains. “It puts a phone in every pocket but it's not Apple or Samsung, it puts shoes on the feet of the world, but it's not Nike or Adidas, it gives the world wings, but it's not Red Bull or Boeing.”
SAP’s Enterprise Cloud Services portfolio empowers customers to run a modern, intelligent ERP system in the cloud, enabling them to become cost-effective and sustainable intelligent enterprises.
One aspect of this portfolio is RISE with SAP, a business transformation-as-a-service platform that enables every company to become an intelligent and sustainable enterprise. “This is practically the vehicle to deliver SAP's Intelligent Enterprise Vision,” Costea adds. “It brings together the solutions and services you need, in one package, regardless of where your business stands now or where you want it to go.”
RISE with SAP enables businesses on their transformation journey
Launched in January 2021, RISE with SAP helps companies seize the advantages of cloud computing in their mission-critical, core systems.
“The first thing that a customer needs for true business transformation is simplicity,” describes Costea. “That means having only one company which is responsible for service-level agreements, operations and issue handling. That comes with the benefit of best-of-breed cloud infrastructure providing a native cloud landscape powered by SAP and our hyperscaler partners.”
Second, they need a guided journey. “SAP is with them on each step of their road to an intelligent enterprise, migrating from the current ERP environment with tailored training, tools and services,” Costea explains.
“And third, they definitely need accelerated premier value, which truly transforms all aspects of their business without high upfront investments. That makes them more resilient, profitable, and sustainable by adopting best practice processes and industry next-generation practices.”
With SAP’s Enterprise Cloud Services continually growing, when it comes to securing the RISE with SAP platform innovation is essential.
“Enterprise Cloud Services growth has been impressive in the last two years, and we look forward to continued growth,” Costea comments. As a result, this growth means onboarding top customers from all industries with the strongest security requirements.
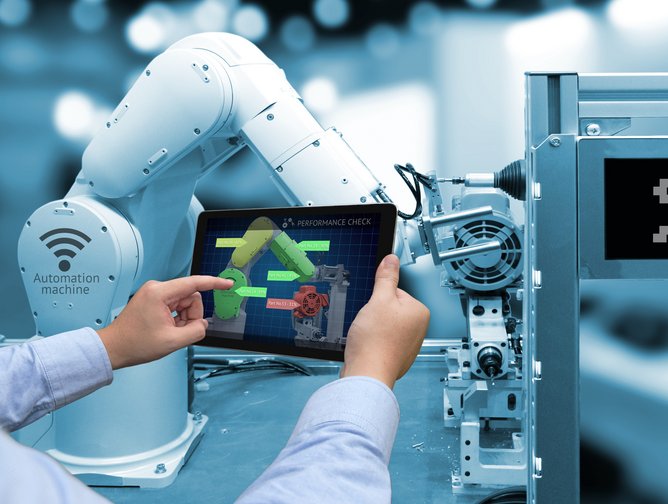
“With that in mind,” he adds, “we need to innovate in the automation space in order to become more efficient and faster in processing big amounts of data, in creating detections, in tuning them, in making sure all the security controls are enforced at the deployment level and at the same time offering the visibility and transparency all these customers need.”
Securing RISE with SAP
When it comes to securing RISE with SAP, Security Engineering, Detection, Monitoring and SOAR each play a key role. SAP’s Security Information and Event Management system is the core of the organisation’s Security Operation Centre, with Costea’s team working with one of the top software security providers to create the platform for SAP’s cloud. “In addition, SOAR components are integrated with our SIEM in order to support our security operations in the most efficient way,” he adds. “But that still is not enough.”
Central to Costea’s approach to security is speed. From that perspective, his team faced five main challenges.
“First,” he explains, “we needed the ability to easily manage data normalisation and enrichment to ensure the security triage team has the proper context and details to make quick decisions.
“Second, we needed a way to consistently measure our ability to detect priority threats across the MITRE ATT&CK framework in real-time and ensure we have a proper understanding of where and how we need to improve.
“Third,” Costea adds, “we had to streamline how detections are managed, deployed, and version controlled, while also improving the time to deploy them.
“Fourth, we had to improve our triage and analysis capabilities by understanding correlation relationships fast. And fifth, we use several tools in our Detection Lifecycle, and we were looking for a way to centralise everything.”
That, Costea adds, is where SAP’s work with the automated threat detection platform Anvilogic comes in, “which helps us to address these five challenges.”
A focus on zero trust
The rapid adoption of cloud services in recent years brings a new focus on Zero Trust principles. Organisations can no longer trust perimeter security alone with an “implicit trust” granted to assets or user accounts based solely on their physical or network location.
Most cyberattacks and data breaches come as the result of a stolen identity, and while more and more corporations are using identity protection solutions, this type of protection is not built into the architecture. Zero trust is designed to solve these shortcomings.
“SAP applications are business-critical applications for many enterprises and all of them think about two main use cases in regard to zero trust: to make connections between SAP solutions zero-trust compliant, and to facilitate more secure user access and accelerate migration to cloud solutions from SAP,” Costea explains.
“We work with Zscaler for RISE with SAP S/4HANA Cloud, public or private editions and SAP S/4HANA Cloud, private edition.”
The need for data observability
As Costea explains, when it comes to SAP’s security strategy speed alone is not enough: “We also need to have control and visibility into our own datasets so that we make intelligent decisions.”
Central to this is SAP’s collaboration with observability pipeline Cribl.
“We collect and process tens of terabytes of data per day, and that amount of data flows over some big highways in the city of SAP, and Cribl gives us the control over the lights, over the crossroads, over when do I want to close a highway or not.Because the private cloud is an extension of our customer's network, they feel like we are part of their network, and they want to have a bit more visibility into what this cloud service delivers for them from a security perspective,” Costea explains. “As a result, we decided to create specific data flows for customers interested in getting their log service in a controlled way, with the correct architecture built around what we call Customer Data Landing Zones. Speeding onboarding, enrichment, normalisation and masking features provide us with clean, relevant data on which to build better alerts and have data ready to accelerate incident investigation and response.”
Autonomous Application Exploit Engine as a service
Finding vulnerabilities and managing them in an environment that is already filled with new, emerging, and evolving threats can be overwhelming. The sheer volume of available patches that must be deployed each month is already massive and it continues to grow.
“In the context of SAP Private Cloud, the customer still keeps the ownership and responsibility to secure the application layer,” Costea describes. “That means on one side that the customer needs to cooperate with us in approving specific downtime windows, and on the other hand that they have a role in analysing product-related patches released by the SAP Product Development Teams.”
One of SAP’s new services, RAVEN, which will be launched as a pilot end of 2023, has a component developed with CODA that will allow customers to make decisions with speed and accuracy when it comes to managing risk.
As Costea explains, the service will deliver hyper-contextualised risk signals to customers, allowing them to take the correct and timely decisions when it comes to managing risk across their SAP cloud environments.
“Our goal at SAP is to build solid processes, leveraging bleeding-edge technology in order to help our customers reduce their real cyber risk exposure to nearly zero,” he adds. “And we know this requires continuous effort from all parties involved.”
AI and ML present new risks in the security landscape
The deployment of emerging technologies such as AI and ML are becoming increasingly common in automating and streamlining various processes. However, as Costea explains, these technologies present new risks, as they may become targets for attackers. “New vulnerabilities or zero-day exploits may be identified in these systems, which must be considered,” he comments. “Another area of concern is the security of the Internet of Things, which has gained momentum in the market in recent years”.
As companies continue to adopt container-based architectures, container security, and Kubernetes-based security in the cloud are also emerging as important topics on the cybersecurity agenda. “Overall,” Costea adds, “it is important to remain vigilant and proactive in identifying and addressing potential risks associated with these new technologies.
Quantum computing is another emerging trend that presents significant challenges to cybersecurity, with its potential to operate at much faster speeds than current technology meaning that current encryption methods may be compromised. “Encryption algorithms that were once deemed secure may become vulnerable in a matter of days, weeks, or months, rather than years,” Costea concludes. “These challenges require the industry’s attention in the coming years to maintain the security of sensitive data and systems.”